Cyber-Criminals Change Tactics to Exploit #COVID19
- September 21, 2020
- Article, Business advice
The COVID-19 pandemic has led to a significant shift in tactics employed by cyber-criminals, according to Bitdefender’s Mid-Year Threat Landscape Report 2020, published today.
Threat actors have heavily focused on the issues related to the pandemic to launch attacks such as phishing, ransomware and malware as well as exploit the increased reliance on home networks and IoT devices in the lockdown period, the study found.
Bitdefender also revealed it had received a five-fold increase in the number of coronavirus-themed reports in the first two weeks of March alone, while an average of 60% of all received emails was fraudulent in April and June. Overall, an average of four out of 10 COVID-themed emails was tagged as spam throughout the first of half of 2020. These frequently impersonated government, health and financial institutions to spread misinformation, fake cures and offer for protective equipment.
As the shift to home working took place due to COVID-19 lockdown restrictions, cyber-criminals adapted their strategy to target this phenomenon. This included the discovery of a new DNS hijacking attack targeting a popular brand of home routers that redirected victims to malware-serving websites promising applications that offer new and up-to-date information about the outbreak.
In addition, malware developers also quickly sought to target applications commonly used by remote employees, such as the Zoom video conferencing platform.
Suspicious incident reports related to IoT devices went up by 46% in the six months from January to June, which is linked to people staying indoors much more during the lockdown period. Over half (55.73%) of IoT network threats involved port-scanning attacks.
Ransomware was another particularly popular mode of attack in this period, with a seven-fold year-on-year increase in reports.
Speaking to Infosecurity, Liviu Arsene, a global cybersecurity researcher at Bitdefender, explained that he expects cyber-criminals to continue leveraging the COVID-19 pandemic to launch attacks throughout the rest of 2020. “If during the first half of 2020 cyber-criminals have been exploiting the pandemic with messages promising miracle cures and medical devices or equipment meant to protect users from infection, during the second half we’ll likely see attackers exploiting the economic and social aftermath of the pandemic,” he said.
“Spam or fraudulent messages will likely exploit the way both private and public companies have changed their interaction with users. For example, messages claiming to be from financial institutions asking customers to update their personal and financial data or promising financial relief, because they can no longer do it in person in light of COVID-19 restrictions.”
We’re KDI
Get advice, service and products that fit your unique needs. KDI is an expert partner for complete IT Services and Networking Support based out of the Greater Vancouver area. We are your one-stop IT solution, uniquely combining aspects of information technology, software development, and accounting expertise to make your work life easier.
Visit our contact page, send an email to info@kdi.ca or give us a call on (604) 574 7225.
News Source: https://www.infosecurity-magazine.com/
About us and this blog
Kobelt Development Inc. is an information systems support company which provides top quality and consistent client care.
Contact Us
At KDI we offer excellent customer service to clients all the while making their lives easier and simpler through the use of information technology.
Subscribe to our newsletter!
Site content
Recent Posts
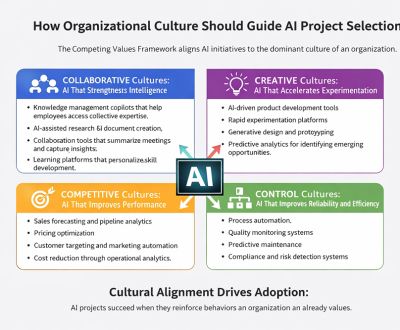
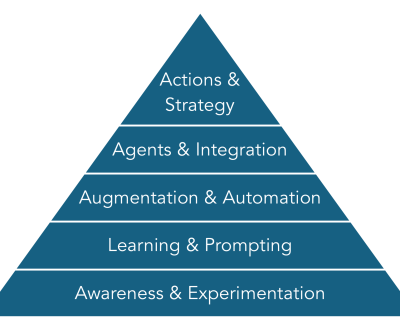
- Introduce AI in Any Organizational Culture April 1, 2026
- How Organizational Culture Should Guide Project Selection March 25, 2026
- Keeping Legacy Systems Running — While You Plan What’s Next March 24, 2026